
Cybersecurity has become paramount for businesses and individuals as digital transformation, internet usage and digital asset values are skyrocketing.
Thailand encountered more than 20 million cyberthreats last year, according to global cybersecurity company Kaspersky.
Kaspersky Security Network (KSN) reported its products detected 20,598,223 different internet-borne cyberthreats on computers using KSN items in Thailand last year. Some 28.4% of Thai users were at risk of infection from online threats last year.
Thailand ranked 87th worldwide when it comes to the dangers associated with surfing the internet. Among its Asean peers, the Philippines was sixth, Malaysia seventh, Vietnam 19th, Indonesia 66th and Singapore 154th.
For web threat detections against consumers and businesses, data shows 2.7 million detections on consumer products and 856,000 detections on corporate products in Thailand.
Thailand ranked fifth in Asean for highest level of consumer detection, and third for highest level of business detection.
Kaspersky said its products detected 49.9 million local incidents on computers using KSN items in Thailand, ranking 70th worldwide.
The share of incidents caused by servers hosted in Thailand stands at 0.01%, which represents 273,458 incidents.
Thailand ranks 56th in this category worldwide.
The firm's new report titled "Mobile Malware Evolution 2020" also shows 28,861 mobile malware detections in Thailand last year, ranking the country 44th in this category globally.
RISKS FACING COMPANIES
"The pandemic has blurred the lines dividing corporate defence and home security," said Yeo Siang Tiong, general manager for Southeast Asia of Kaspersky.
"Remote work, online classes and digitalisation across all sectors will continue, at least during 2021, and it is high time for all shapes and sizes of businesses to understand online threats, even against individuals, should be considered as risks against companies."
Mr Yeo said several incidents in the form of scams and social engineering tactics were detected last year, aimed at tricking people and stealing money or information.
Most of the threats, he said, used buzzwords related to Covid-19.
"Avoiding such trickery requires a good deal of calmness and vigilance, which is tough to manage amid the chaos of the pandemic," said Mr Yeo.
Piyatida Tantrakul, Thailand country manager of Trend Micro, an enterprise data security and cybersecurity solution provider, said the company's annual cybersecurity report shows threat actors keep targeting organisations in important sectors.
Government and healthcare operators were persistently attacked by ransomware, said Ms Piyatida.
The company found more than 19 million threats linked with Covid-19, including malicious URLs, spam and malware, she said.
"Trend Micro found significant growth in vulnerabilities that pose potential risks to many organisations," said Ms Piyatida.
Some 1,453 vulnerabilities were reported last year, up 40% from 2019. Of this number, 173 are regarded as a critical level of vulnerability and 983 at a high level.
"Those at the critical level need to be patched as soon as possible," she said.
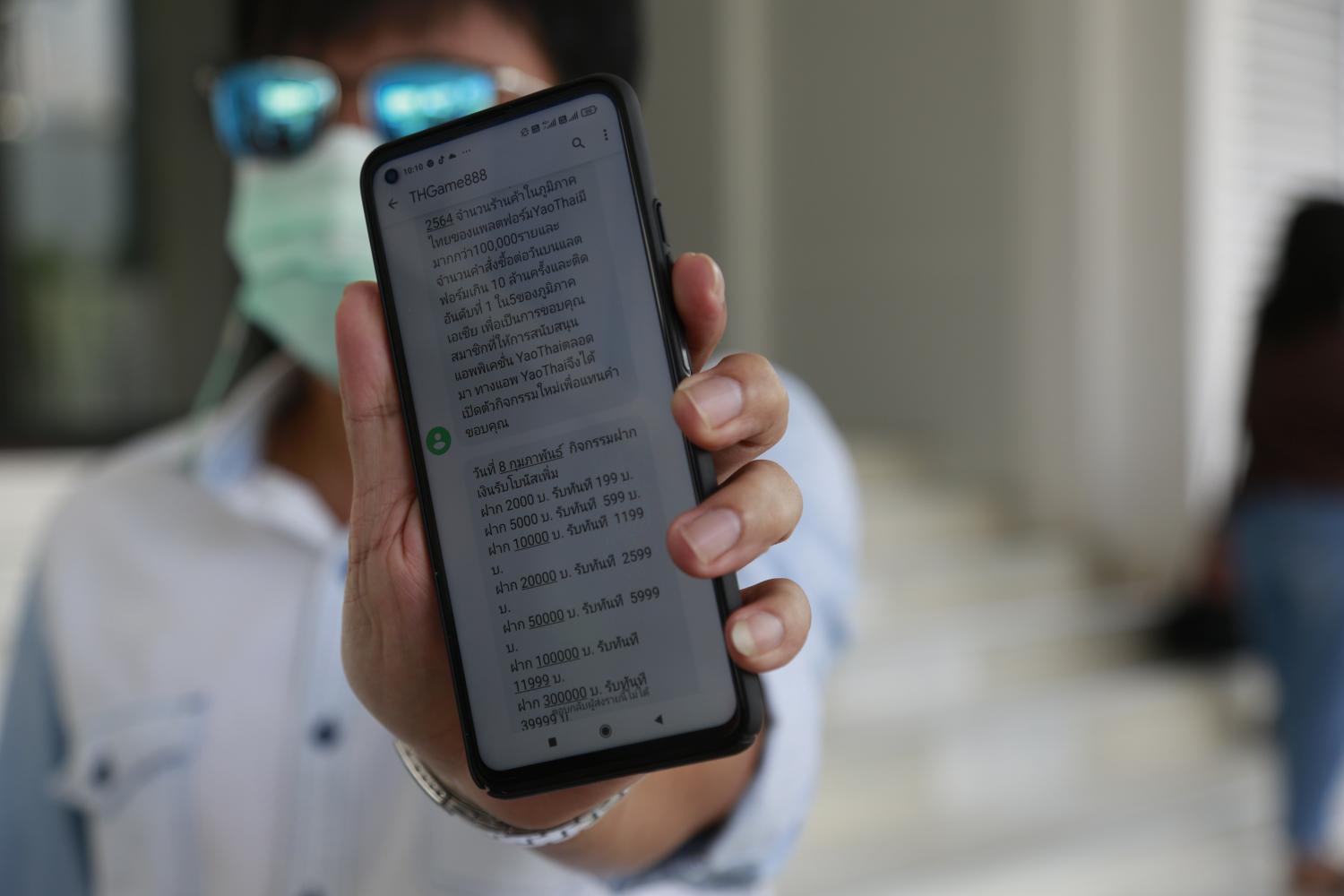
above A man shows an online message trying to trick him into joining a bogus investment through an application. Arnun Chonmahatrakool
BUSINESS DIFFERENTIATOR
Brandon Tan, sales engineering director for Asia-Pacific at Forcepoint, a US developer of computer security software and data protection, said the pandemic led to remote work, cloud deployment and digital transformation.
"Cybersecurity is now a business differentiator," Mr Tan said.
"Cybersecurity has become the enabling engine that permits businesses to accelerate their pivot to the cloud and take advantage of the speed, scale and resilience of digital transformation."
Cybersecurity features include Secure Access Service Edge (SASE), which combines network security functions with wide area network capabilities to support the dynamic secure access needs of organisations.
SASE is delivered primarily as a service and based upon the identity of the entity, real-time context and security or compliance policies.
There is also rising demand for security cloud platforms.
Developers are using security as a tool, but are having to shoehorn in applications and functions not necessarily designed as cloud-native, he said.
"Security will be a cloud commodity, and the combination of technology plus data will give IT leaders true visibility in how and where data is moving through an organisation," said Mr Tan.
"It is this visibility of data which is the game changer. It's not about monitoring in terms of keeping tabs on people's actions, or invading their privacy. It's about giving data analysts and business leaders a clear line of sight over data and its movements."
DATA VISIBILITY
In 2021, data visibility and the management of data protection are believed to be the most important cybersecurity imperatives for enterprises.
As people shift to remote work, it is important to move towards user activity monitoring, an approach that relies on analytics to understand data access patterns and Indicators of Behavior (IoB) that can indicate levels of risk.
"Without visibility of data in this way, we cannot scale and understand how to work productively, flexibly and securely," said Mr Tan. "The combination of behavioural analytics and IoBs form the foundations of dynamic risk assessment."
Data usage must be examined and understood in context, and data loss prevention policies applied adaptively and dynamically.
"If we can create cybersecurity technologies that build upon machine learning and analytics to measure and understand data movements in quasi real-time, we can avoid the upcoming dawn of disappointment on the horizon," he said.

Data protection management is among one of the key cybersecurity imperatives this year. no photo byline
According to Mr Tan, leaders must revisit their policies and processes, validate their posture and risk appetite, and avoid assuming all is well just because they haven't encountered an incident yet.
Longer-term, cloud-native solutions with a deep understanding of users' behaviour will deliver permanent solutions, rather than stopgaps when it comes to protecting data and intellectual property, he said.
BEHAVIOURAL UNDERSTANDING
In 2021, Forcepoint believes machine learning and analytics will fall under tighter scrutiny, as trust in their unbiased nature and fairness as well as ethical boundaries will be questioned, said Mr Tan.
A number of cybersecurity systems use machine learning to make decisions about whether an action is appropriate (or low-risk) for a given user or system. Machine learning must be trained on large enough quantities of data and must be carefully assessed for bias and accuracy.
To build cybersystems that help identify risky users and prevent damaging actions, monitoring of user activity must be done appropriately, and with people's privacy and appropriate ethical guidelines in place, he said.
Understanding how people adapt, respond to and inform their environments is critical for organisations to build behavioural understanding into cybersecurity systems and design security for the human element, said Mr Tan.
SYNTHETIC ID FRAUD
According to consulting firm McKinsey, synthetic ID fraud is the fastest-growing type of financial crime in the US and is spreading to other countries. Synthetic ID fraudsters use real and fake credentials to build a phony profile that is strong enough to apply for credit.
Although the applications are normally rejected by credit bureaus, having a file is enough to set up accounts and start building a "real" credit history to apply for bank accounts, credit cards and loans.
It is almost impossible to tell a real identity from a synthetic one, and because no individual's ID was stolen, the real victims are the businesses left with no way to recover their losses.
Over time, businesses can build a checklist of inconsistencies commonly found on synthetic IDs and use this to train an algorithm to automatically flag suspect files for action.